"Technology Audit – A Key Enabler for Digital Transformation Initiatives. Our Information Technology Audit (TA) Services – © Inspace Business Impact Evaluator (IBIE), has been copyrighted and recognised by HRD Ministry, Government of India for its Audit Methodology and Framework.
What Is Email Phishing?
Email Phishing is a method of trying to gather personal information using deceptive e-mails and websites. This Phishing is a type of cyber-attack that uses disguised email as a weapon. The goal is to trick the email recipient into believing that the message is something they want or need — a request from their bank, for instance, or a note from someone in their company — and to click a link or download an attachment.
Phishing can also be termed as a type of online scam where criminals impersonate legitimate organizations via email, text message, advertisement or other means in order to steal sensitive information. This is usually done by including a link that will appear to take the user to the company’s website to fill in information – but the website is a clever fake and the information provided goes straight to the hackers behind the scam.
The term “phishing” is a spin on the word fishing, because criminals are dangling a fake “lure” (the legitimate-looking email, website or ad) hoping users will “bite” by providing the information the criminals have requested – such as credit card numbers, account numbers, passwords, usernames or other valuable information.
Business Impact – A Sample Scenario
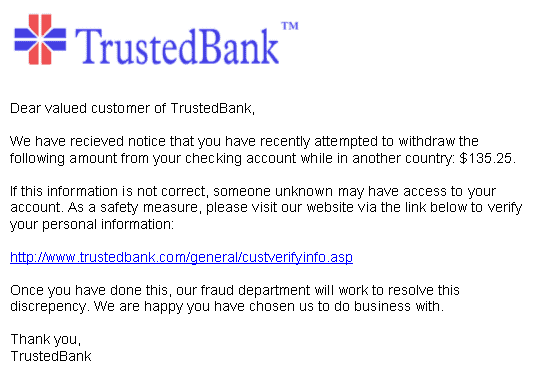
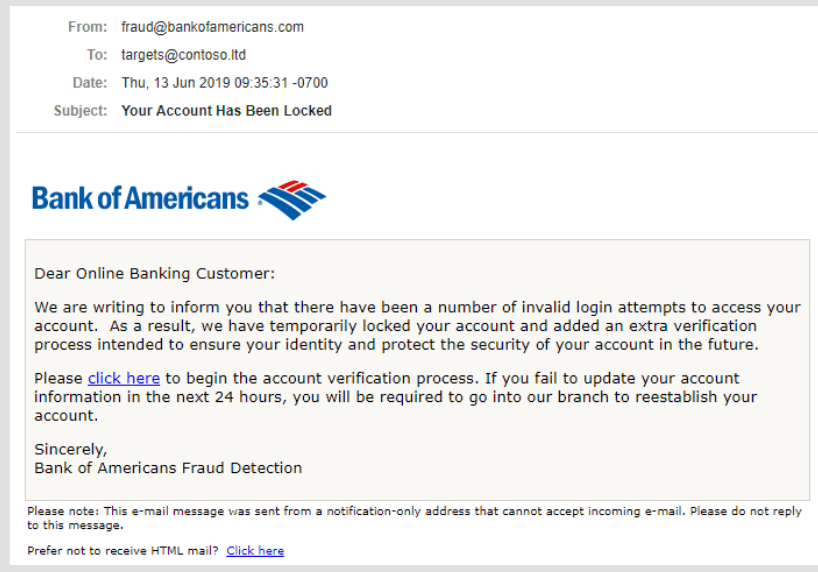
A user may receive a seemingly legitimate mail from their Bank (sample shown below) requesting them to make the banking transaction by clicking a link provided.
When the user clicks the link provided, they are taken to a website, which is in fact a fake website. The user is asked to provide confidential bank information such as username, password or PIN. When the user provides these details, the fake website stores the details to access the users’ bank account funds. This may result in financial loss for the individual account or organisation.
What is Email Phishing Simulation?

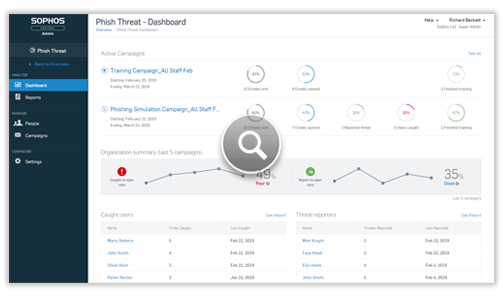
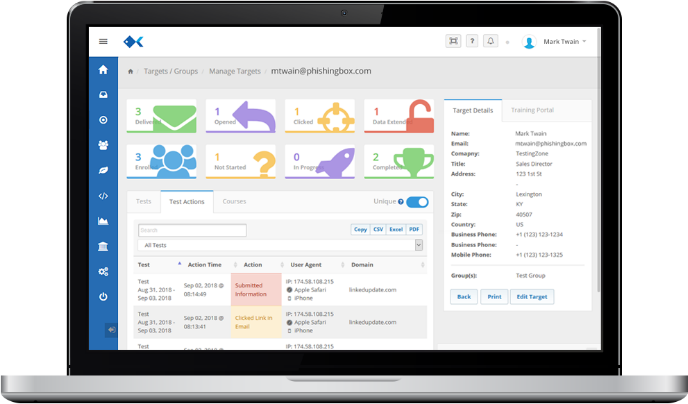
Email Phishing simulation is a program that organizations can use to send realistic phishing email to employees in order to gauge their awareness of attacks and what to do with phishing emails when they receive them. Phishing simulation is typically used in coordination with training that educates employees about how these attacks work and how to avoid them.
A simulated phishing attack uses commonly used and believable email templates that are likely to come in the inbox of an organization’s employee. The emails being sent as a part of a simulated attack closely mimic a real-life phishing attack. Real-life phishing attacks often rely on social engineering to target individuals and businesses. Humans are considered as the weakest link in the cybersecurity ecosystem, and phishing is one of the types of social engineering attacks exploiting this weakness.
Benefits of Email Phishing Simulation
A simulated email phishing attack is a great way to identify the individuals within the organization who are not well versed with good security practices and require additional training. Also, such activity can allow you to measure the effectiveness of your training concerning social engineering attacks. Once this activity is concluded, the report should contain details such as –
- Number of emails opened
- Number of users who clicked on the link
- Number of users who opened the attached file
- Number of users who reported the email
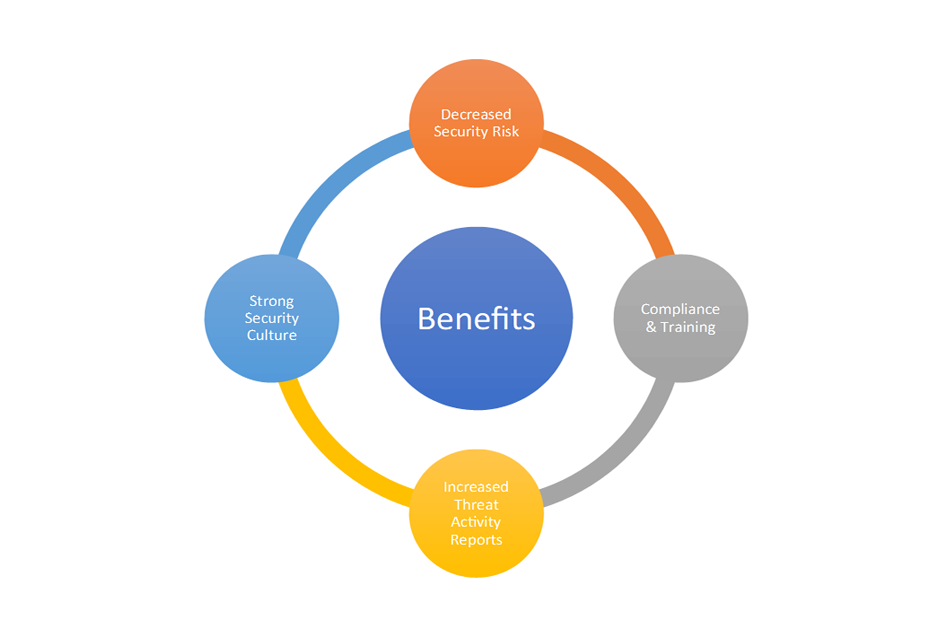
Just like other tools to defend an organization against the incoming attacks, email phishing simulation exercises equip an organization’s employees with the know-how of phishing attacks and how attackers craft genuine-looking emails to fulfil their motives.